Penetration testing in simple terms is a simulation of a process a hacker would use to launch an attack on a business network, attached devices, network applications, or a business website. The purpose of the simulation is to identify security issues before hackers can locate them and perform an exploit.

Ceitcon offers a penetration test, which is a simulated cyber-attack against your computer system to check for exploitable vulnerabilities. Ceitcon Pen testing involve the attempted breaching of any number of application systems, (e.g., application protocol interfaces (APIs), frontend/backend servers) to uncover vulnerabilities, such as unsanitized inputs that are susceptible to code injection attacks.
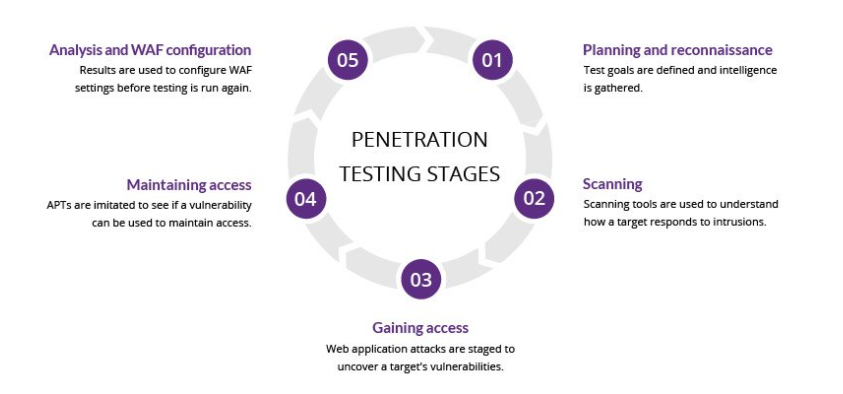
• Defining the scope and goals of a test, including the systems to be addressed and the testing methods to be used.
• Gathering intelligence (e.g., network and domain names, mail server) to better understand how a target works and its potential vulnerabilities.


• Static analysis: Inspecting an application’s code to estimate the way it behaves while running. These tools can scan the entirety of the code in a single pass.
• Dynamic analysis: Inspecting an application’s code in a running state. This is a more practical way of scanning, as it provides a real-time view into an application’s performance.
This stage uses web application attacks, such as cross-site scripting, SQL injection and backdoors, to uncover a target’s vulnerabilities. Ceitcon Team then try and exploit these vulnerabilities, typically by escalating privileges, stealing data, intercepting traffic, etc., to understand the damage they can cause.

The goal of this stage is to see if the vulnerability can be used to achieve a persistent presence in the exploited system long enough for a bad actor to gain in-depth access. The idea is to imitate advanced persistent threats, which often remain in a system for months in order to steal an organization’s most sensitive data
The results of the penetration test are then compiled into a report detailing:
• Specific vulnerabilities that were exploited
• Sensitive data that was accessed
• The amount of time the pen tester was able to remain in the system undetected

Your Ticket Created Successfully
